What is phishing?
Phishing is a way for hackers to gain protected information, tricking people into giving away bank credentials, passwords, and more. That’s why phishing emails are considered a main vehicle for identity theft. They look legitimate, and most people don’t realize it’s a scam until it’s too late. Phishing can be categorised in two different ways:
-General phishing is sent in a blast for multiple people and acts like a boilerplate trying to attract someone to click and enter pertinent information.
-Spear phishing is more direct, and a specific person (or specific group, such as executive, HR, or finance staff) is identified and targeted. The person of interest is sent an email from someone they trust asking for sensitive information. The majority of the time, the email comes from high-profile individuals, such as the CEO emailing someone in the finance department for account information.
Phishing is different to Ransomware. With phishing the reward for the hackers is in the information. The credit card numbers, passwords, and any other information acquired in a phishing attack could be sold to someone else. Phishing attacks can cause more wide-ranging damage than ransomware because your information can be used to give someone a new identity or open up lines of credit in your name. Ransomware is a type of malicious software designed to block access to a computer system until a sum of money is paid.
Email security
How to identify phishing attacks
Recognising attacks are easy when you know what to look for. So let us give you what you should be looking for before you open those E-mails:
The email will be asking for personal information. It might say something like your password has expired, please update it here by clicking this link (directing you to a spoofed website).
Most phishing scams have grammar errors. This could be one misspelled word or random capitalisations in the emails. The errors are usually very subtle, and often resemble something that would have come from a trusted source.
Many phishing emails will have the proper banners e.g. logos, slogans etc edited into the emails to make them more convincing but they may be one or two shades off. This can trick users into thinking they are corresponding with Barclays, GOV.UK etc.
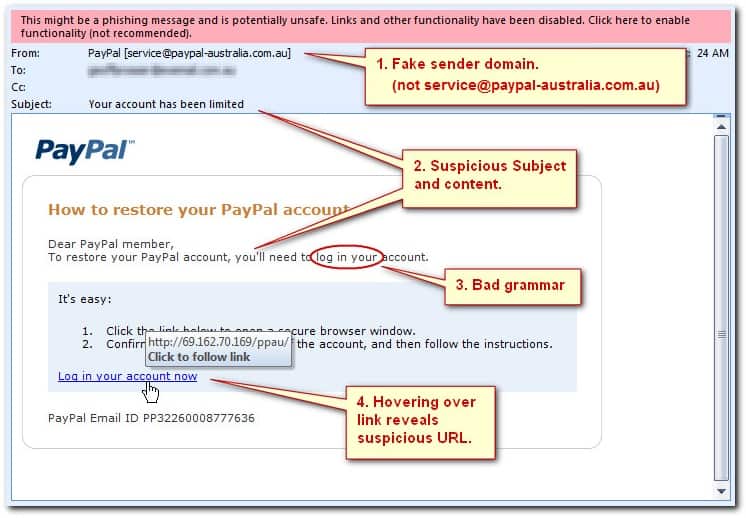
The hyperlink (a link that takes you to another website/document) goes somewhere else. Anyone can change the hyperlink in an email to say something completely different e.g the Hyperlink could be for google.co.uk but it could be worded as ‘Google’ and it will take you to the same place but if you hover over the hyperlink with your mouse, it will give you the full web address it is taking you to. A good way to check if they are really taking you where you should be!
Best Practices
Everyone receives phishing emails (156 million phishing e-mails are sent approximately each day), so protecting yourself from an attack is important. Follow these best practices to reduce your chances of falling for a phishing scam.
Keep phishing training up to date. Have your practices and employees learn to familiarise themselves with threats. Educated users are harder to trick.
Don’t click on any suspicious emails. If you’re not expecting an email—don’t click! Instead check with the individual it came from (e.g. contact them on the phone or send them an instant message) and confirm the request before sending personal information. If the email is from a bank or another organisation, navigate to their website in a separate browser to make sure you are going to the correct website that are asking you to visit.
Take the time to look at the details. Phishing scams are so detrimental because if you miss one simple spelling error or don’t check a link, you could be in trouble. Most scams come from places you would normally trust, causing you to fill in the information without thinking about it. This is how cybercriminals prey on your trust.
Ensure that your email system uses spam and virus filters. Systems like Hosted Exchange, Gmail for Work etc, not many systems can catch everything but try and ensure mail is scanned before it hits your inbox.



